Zero Knowledge Password Managers: How To Protect Your Vault When Your Provider Gets Hacked
Only 36% of US adults use password managers, yet users who do are nearly half as likely to suffer credential theft compared to those who do not, which shows how critical these tools are when they are built on true zero knowledge architecture and paired with strong anonymity practices.
.png)
Zero Knowledge Password Managers: How To Protect Your Vault When Your Provider Gets Hacked
Only 36% of US adults use password managers, yet users who do are nearly half as likely to suffer credential theft compared to those who do not, which shows how critical these tools are when they are built on true zero knowledge architecture and paired with strong anonymity practices.
Key Takeaways
QuestionAnswerWhat is a zero knowledge password manager?It is a password manager that encrypts all secrets locally so the provider cannot see, reset, or recover your vault. Even during a breach, attackers and the provider should only see ciphertext. Our focus at Blockd follows the same zero knowledge principle for messaging, not passwords.Why does anonymity matter for password managers?Because your metadata trail can expose who you are, what you use, and when you log in. We argue in our metadata deep dive that true privacy requires breaking this identity link, not just encrypting contents.Can zero knowledge protect you in a provider breach?Yes, if implemented correctly. As we describe in our security model, zero knowledge means compromising servers does not reveal plaintext—only encrypted blobs tied to secrets only you hold.Is encryption alone enough?No. Encryption without metadata and identity protection is incomplete. In our view, outlined in our privacy manifesto, anonymity and minimal data collection are just as important as cryptography.How is Blockd relevant if it is not a password manager?Blockd applies the same zero knowledge and anonymity principles to messaging that advanced password managers apply to vaults. We design so that we cannot read your content or meaningfully identify you, which is the same standard password managers should hold.Do I still need strong master passwords or passkeys?Yes. Zero knowledge protects against provider abuse and server breaches, but weak master passwords or poor device security will still expose your vault, which is why we advocate strong, device-bound credentials and user control over keys in any system.
1. Why Zero Knowledge Is Non-Negotiable For Password Managers
Password managers centralize your entire digital life in one vault, which makes their security model either your strongest shield or your single point of catastrophic failure. Zero knowledge architecture is the line between a breach that leaks everything and a breach that yields unreadable noise.
In a zero knowledge design, encryption happens on your device before anything touches the provider’s infrastructure. The provider never sees your master password, never holds your decryption keys, and never has the technical ability to read your passwords.
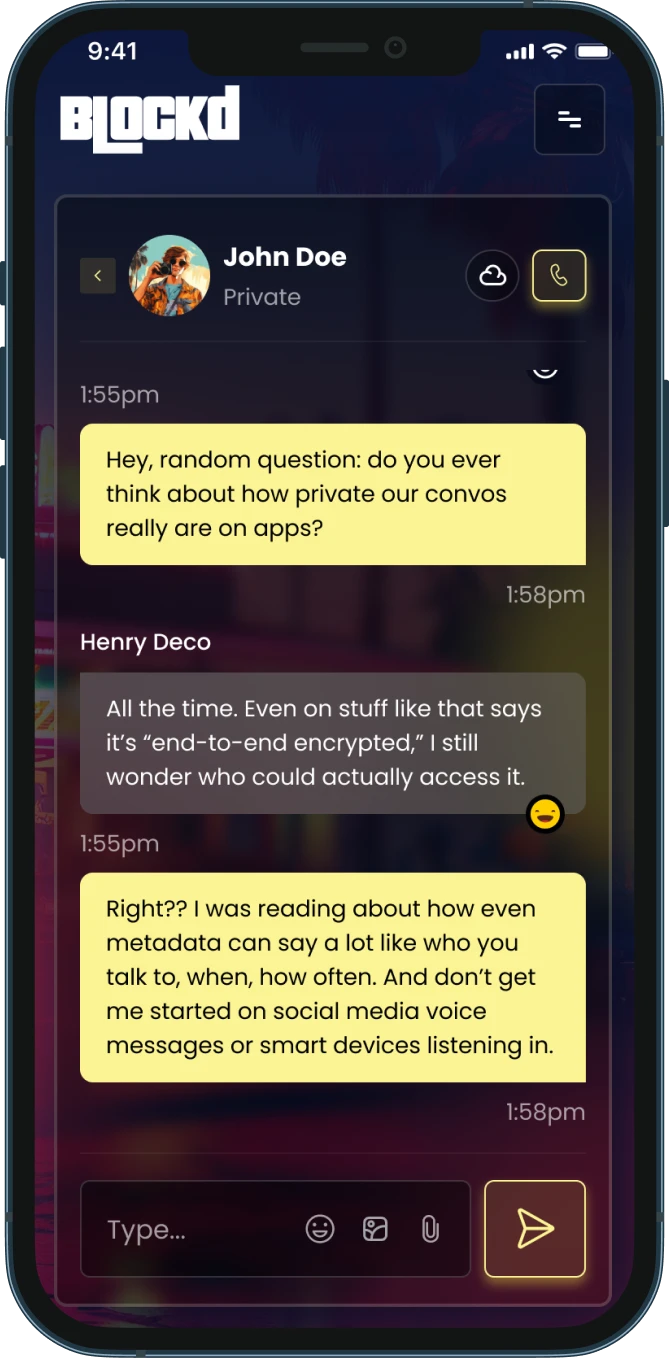
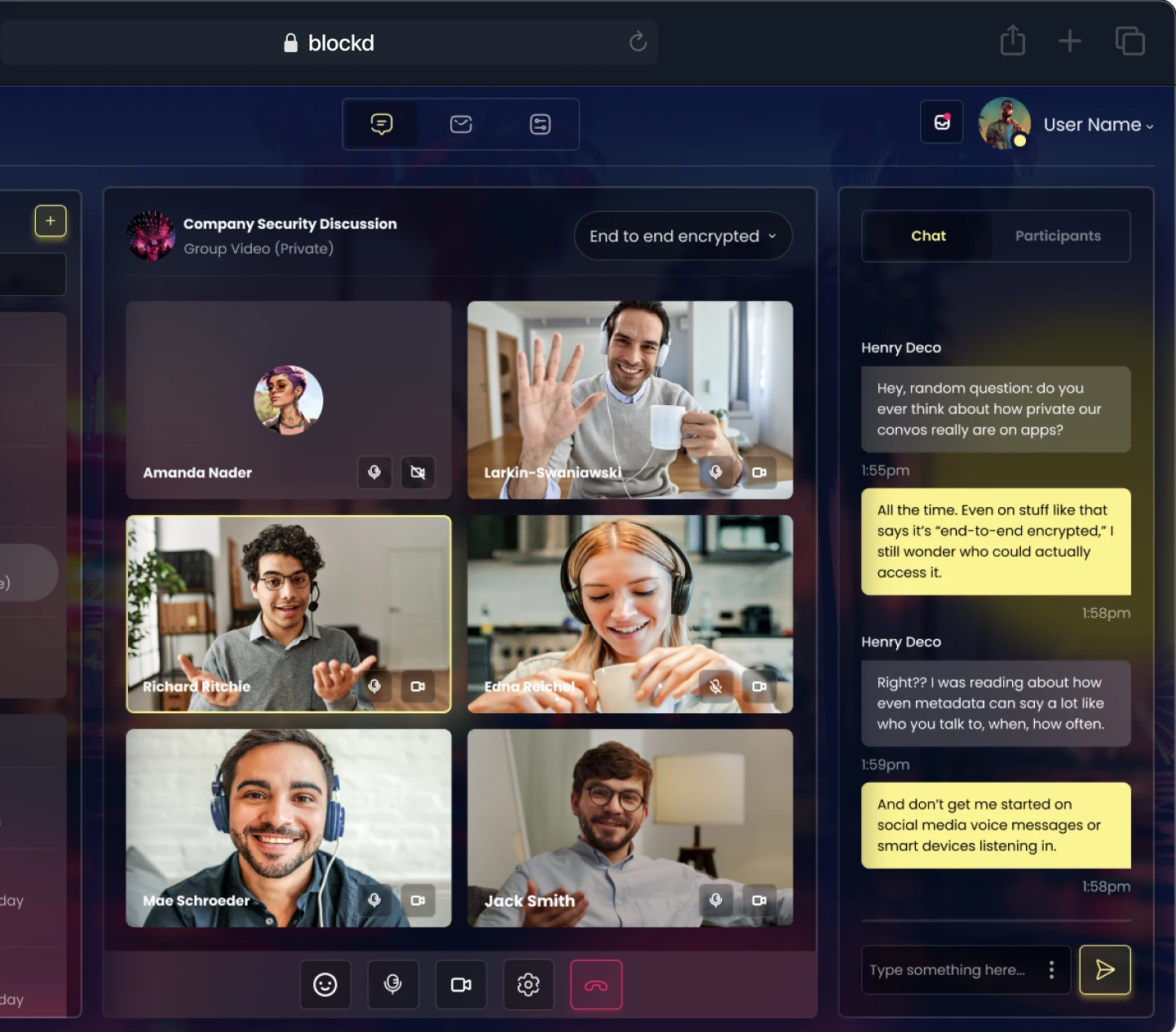
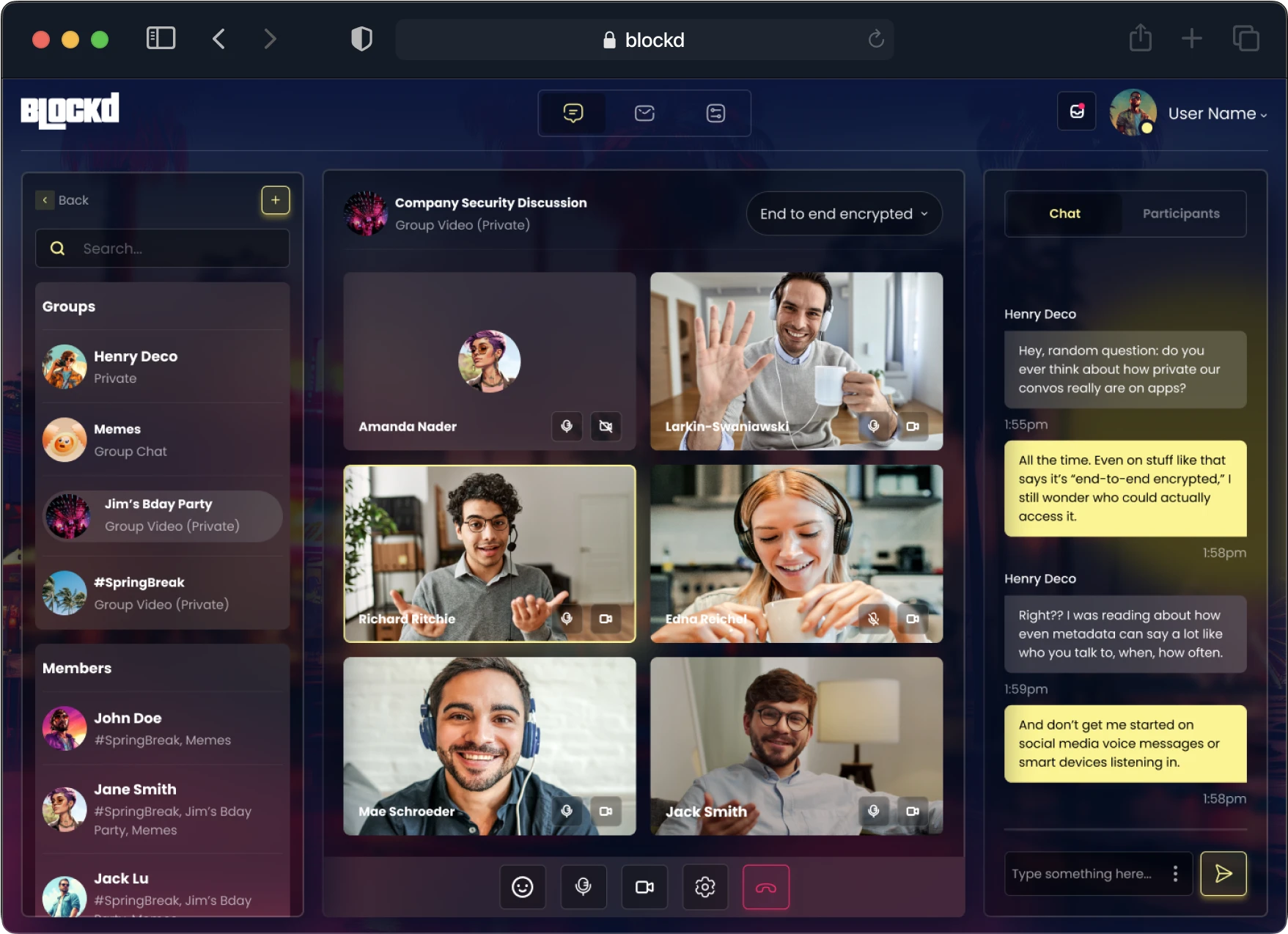
We apply this same pattern in Blockd for messaging: content is encrypted at the edge, and decryption keys live with you, not with us. The provider becomes a blind courier that shuttles ciphertext while remaining permanently excluded from the conversation.
This is the standard every serious password manager should adopt. Anything less is asking users to hand over the keys to their own lockbox.
2. How Zero Knowledge Password Managers Actually Work
Zero knowledge in password managers is not a slogan—it is a set of design decisions. At the core is client-side key derivation, where your master password is processed locally (often with a slow key-derivation function) to generate an encryption key that never leaves your device.
Your vault contents are encrypted with this key before syncing to any server, so what sits on the provider’s infrastructure is only ciphertext and metadata. When you log in from another device, the same derivation happens locally, and only then can your vault be decrypted.

Bitwarden, for example, explicitly states that it uses zero knowledge encryption as its core security model, with data encrypted locally and the master password never transmitted. Bitwarden’s servers are designed so operators cannot decrypt or alter user vaults—this is the right threat model.
In Blockd, we mirror that posture in messaging. Our zero knowledge architecture and DarkMesh Protocol are designed so that compromising our infrastructure does not expose message content or long-lived keys.
3. Lessons From Breaches: When Zero Knowledge Meets Reality
Zero knowledge architecture is tested in the worst moments, not the best marketing. The 2022 LastPass incident is a useful case study because it was a large-scale breach of a password manager that publicly claims a zero knowledge model.
Roughly 1.6 million user accounts had data exposed, and regulators later fined LastPass, yet the company stated that sensitive customer vault data was encrypted using zero knowledge principles and could only be decrypted with a unique key derived from each user’s master password.


This matters because it illustrates a brutal but important truth: with proper zero knowledge design, a provider breach does not automatically equal immediate plaintext exposure—but weak master passwords and weak key stretching can still be exploited offline.
We architect Blockd under the same assumption: attackers, state actors, or the provider itself may eventually be compromised. The only rational design is one where that compromise still leaves your encrypted data unreadable.
Did You Know?
Users with password managers were less likely to experience identity theft or credential theft in the past year: 17% vs. 32% for those without.
4. Anonymity: The Missing Layer In Most Password Managers
Most password managers talk about encryption, but very few talk about anonymity. Your vault can be encrypted, yet your identity, device fingerprints, IP addresses, and login patterns can still be logged, profiled, and linked to you.
In today’s surveillance environment, that metadata trail can expose who you are, what services you use, and where to pressure you. True privacy needs more than ciphertext—it needs to break the link between your real-world identity and your digital tools.
We build Blockd around that reality. We do not use phone numbers or email addresses as identifiers, and we do not require KYC that ties your account to a real-world identity, because the moment you do that, you create a permanent bridge between a person and their metadata trail.
The same mindset should apply to password managers. If your password manager is deeply integrated with a broader identity platform that collects extensive telemetry, your vault might be encrypted—but your behavioral footprint is not.
5. Zero Knowledge Architectures In Practice: Bitwarden, LastPass, And Beyond
When we talk about password managers focusing on zero knowledge architecture, we are describing a clear trend. Providers increasingly understand that anything short of zero knowledge is unacceptable, and customers are learning to demand it.
Bitwarden’s model is straightforward: it uses zero knowledge encryption, performs key derivation on the client, and emphasizes transparency through open architecture and third-party assessments.
LastPass, despite its breach, demonstrates another point: zero knowledge can reduce the blast radius of incidents, but only if master passwords are strong and key-stretching parameters are aggressive enough to resist offline cracking.
We take a similar layered view at Blockd: encryption must be paired with strong key derivation, robust client implementations, and protocols that minimize metadata—or the “zero knowledge” label becomes a fragile promise.
6. Metadata Trails: Your Real Attack Surface
Even the best zero knowledge vault leaks metadata if the architecture does not explicitly defend against it. That includes login times, IP addresses, device identifiers, and sync patterns—which can all be harvested and correlated.
An attacker does not always need your passwords when they can map your life by watching where and when you authenticate.
In Blockd, we address this in messaging through Tor-based routing and DarkMesh, which splits knowledge across multiple relays so that no single node can see both who you are and who you talk to. Password managers that claim to be privacy-first should be thinking similarly about network-level protections.
If your password manager demands phone-based sign-in, logs your IPs, and ties your activity to a monetized identity graph, then your secrets may be safe while your identity is not.
Did You Know?
77% of password manager users install their vault on multiple devices.
7. Device Trust, Passkeys, And Quantum-Resistant Crypto
Password managers live at the intersection of cryptography and device security. Zero knowledge protects data at rest and in transit, but the endpoint where decryption happens is still a critical weak point.
This is why passkeys and on-device credentials matter. They allow authentication bound to hardware, with keys stored in secure enclaves rather than shared secrets that can be phished or reused.
In Blockd, we pair zero knowledge encryption with a quantum-resistant NaCl-based stack and plan for a world where classical cryptography is not enough. Password managers should be thinking similarly—especially for high-risk users whose vaults will remain valuable targets for decades.
Designs that rely on centralized recovery or weak second factors to “simplify” user experience chip away at the security that zero knowledge offers.
8. Recovery Without Backdoors: Seed Phrases And User-Owned Keys
Recovery is one of the hardest problems in zero knowledge systems. If the provider genuinely has no access to your vault keys, they genuinely cannot rescue you if you lose your master credentials.
Many password managers quietly solve this by retaining some form of reset capability, which incidentally gives them potential access they claim not to have. That is not real zero knowledge—it is a compromise.
The alternative is user-held recovery: seed phrases and secret backups you control entirely. In crypto systems, seed phrases are standard because they remove centralized recovery while still giving users a way back in.
Our philosophy at Blockd aligns with that: you should decide where your keys live, how they are backed up, and whether a backup exists at all.
9. Centralized Giants Vs Independent Zero Knowledge Managers
Google and Apple together control more than 55% of the US password manager market, largely through built-in browser and device features. For many users, these are the default vaults.
Some built-in managers adopt strong encryption and even partial zero knowledge techniques, but they remain embedded in large ecosystems with extensive identity infrastructure, telemetry, and cross-product tracking.
If your goal is pure convenience, that may be acceptable. If your goal is privacy and anonymity, tying your password vault to your primary identity provider is in direct conflict with that goal.
10. How We Apply Zero Knowledge And Anonymity At Blockd (And What Password Managers Can Learn)
Blockd is not a password manager, but the problems we solve are the same class of problems: storing sensitive data, routing it across hostile networks, and preventing anyone—including us—from reading it or linking it to your real identity.
Our zero knowledge architecture means end-to-end encryption with keys we never see, quantum-resistant cryptography, and secure re-encryption of message histories so old data does not stay in a readable state on your device longer than necessary.
We route traffic through Tor or Blockd relays, so there is no single point in the network that knows both who you are and what you are sending. We avoid KYC, phone numbers, and emails because anonymity is not a luxury—it is a prerequisite for real privacy.
Password managers that want to live up to “zero knowledge” should take the same hard line: no backdoor recovery that secretly depends on provider-held keys, no identity requirements that expose users, and no logging that can reconstruct someone’s life out of metadata alone.
Conclusion
Zero knowledge architecture is not a marketing checkbox for password managers—it is a commitment to structural ignorance. The provider must be unable to read, reset, or quietly export your vault, even under pressure.
Encryption, however, is only half the story. Without anonymity, minimal metadata, and user-owned recovery, your identity remains exposed even if your passwords do not.
At Blockd, we apply these principles to messaging, but the same standards should govern every password manager that claims to protect you: no logs to leak, no identities to unmask, and no central authority with the power to see inside your life.
In a world where surveillance is the default, choosing tools that are both zero knowledge and anonymity-respecting is no longer optional. It is how you stay private, stay safe, and stay invisible.
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)






_thumb.png)