DarkMesh Explained: 10 Game-Changing Benefits Of Truly Untraceable Messaging
34% of Americans experienced at least one data breach in the past year, and most of those people were using “encrypted” apps they thought were safe. In a world where your metadata, identity, and devices are constantly profiled, the DarkMesh Protocol exists to make your communication not just private, but effectively invisible.
.png)
DarkMesh Explained: 10 Game-Changing Benefits Of Truly Untraceable Messaging
34% of Americans experienced at least one data breach in the past year, and most of those people were using “encrypted” apps they thought were safe. In a world where your metadata, identity, and devices are constantly profiled, the DarkMesh Protocol exists to make your communication not just private, but effectively invisible.
Key Takeaways
QuestionAnswerWhat is DarkMesh Protocol in Blockd?DarkMesh is the hidden routing and security layer inside Blockd that keeps your messages untraceable, your identity invisible, and your data out of reach, even from us.How does DarkMesh keep messaging untraceable?It combines zero-knowledge architecture, decentralized relays, and Tor-inspired onion routing, as detailed in this deep dive into DarkMesh, so no single party can reconstruct who you are talking to or when.Why is anonymity essential for privacy today?Traditional apps tie you to phone numbers, emails, and KYC identifiers, which creates a permanent metadata trail. DarkMesh, and our decision to require no phone number or email, cuts that link so your messages cannot be bound back to a legal identity.Is Blockd just encrypted, or is it truly anonymous?Encryption protects content, but not who you are or when you talk. Our metadata-focused protections and DarkMesh routing are built to defend both.How does Blockd avoid data breaches?We minimize what exists in the first place. As outlined in our protection model, keys stay client-side, we do not keep central logs, and DarkMesh avoids single points of failure.Can DarkMesh traffic be censored or blocked?DarkMesh uses decentralized infrastructure, and can route via the public internet or the Tor network, which makes surveillance and censorship significantly harder, as summarized on our How It Works section.Who is DarkMesh built for?For anyone who refuses to trade their identity and metadata for convenience, and wants a configurable platform described in our Why Blockd overview, where anonymity and control are standard, not premium extras.
1. What Makes DarkMesh Different: Untraceable By Design
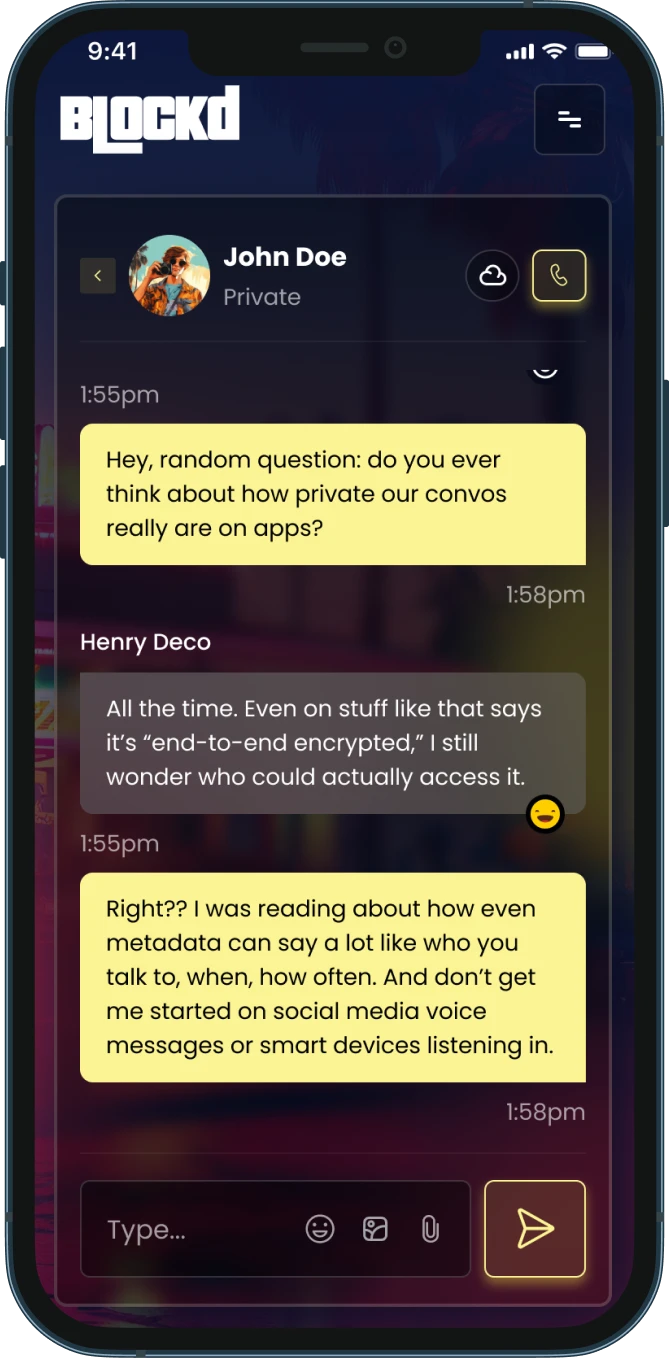
Most messaging apps encrypt content, then expose everything else through phone numbers, IP logs, and behavioral metadata. DarkMesh approaches the problem from the opposite direction, by assuming every observable signal can and will be used against the user.
Our protocol is not a marketing layer on top of a centralized service. It is the core substrate that decides where your packets go, how they look, who can see them, and how little they reveal at every hop.
DarkMesh: Invisible Infrastructure For Blockd Messaging
Inside Blockd, DarkMesh is responsible for making users effectively invisible to observers, including us. It uses zero-knowledge principles, meaning the network can function and route your traffic without needing to know who you are or what you are sending.
That is how we can confidently state that privacy is not a feature in Blockd—it is the foundation the entire platform stands on.
Key Architectural Choices That Matter
- No phone numbers, no email, no KYC required to use Blockd, so DarkMesh never starts with a real-world identity.
- Zero-knowledge architecture so servers handle encrypted blobs, not readable messages or linkable identities.
- Decentralized relays so no single server can map sender, recipient, and timing together.
This combination closes the usual gaps where “secure” messaging apps leak the most: sign up, device fingerprinting, and metadata trails.
2. Zero-Knowledge Architecture: Messages Even We Cannot See
Every private system should start from a simple premise: if we do not have it, no one can steal it from us. DarkMesh operationalizes that through zero-knowledge architecture across messages, identities, and most crucially, metadata.
When you send a message through Blockd, DarkMesh ensures it is encrypted, hashed, and salted before it ever touches a relay, so intermediaries see opaque blobs, not patterns or content.
How Zero-Knowledge Protects Your Conversations
Traditional apps can claim end-to-end encryption while still holding keys, logs, or unencrypted backups. In our system, keys live on your device, and we do not retain server-side material that would let us decrypt your traffic.
We also re-encrypt message data when your conversation is closed, so even if someone seized one of your devices, older content is not just sitting there in plain view.
- End-to-end, quantum-resistant encryption built on NaCl, designed to withstand emerging cryptographic threats.
- Passkeys stored on-device, superior to passwords or typical 2FA that often centralize risk in email or SMS.
- Seed phrase account recovery, similar to crypto wallets, so you are not forced back into phone or email verification.
Nothing To Breach Means Nothing To Lose
Data breaches keep happening because companies collect more than they need, then store it indefinitely. Our approach with DarkMesh is minimal collection and aggressive limitation of what can be inferred, even if a relay is compromised.
If an attacker targets us, there are no central logs that reveal who you are or who you spoke with. Privacy is enforced by the absence of exploitable data, not by policy promises.


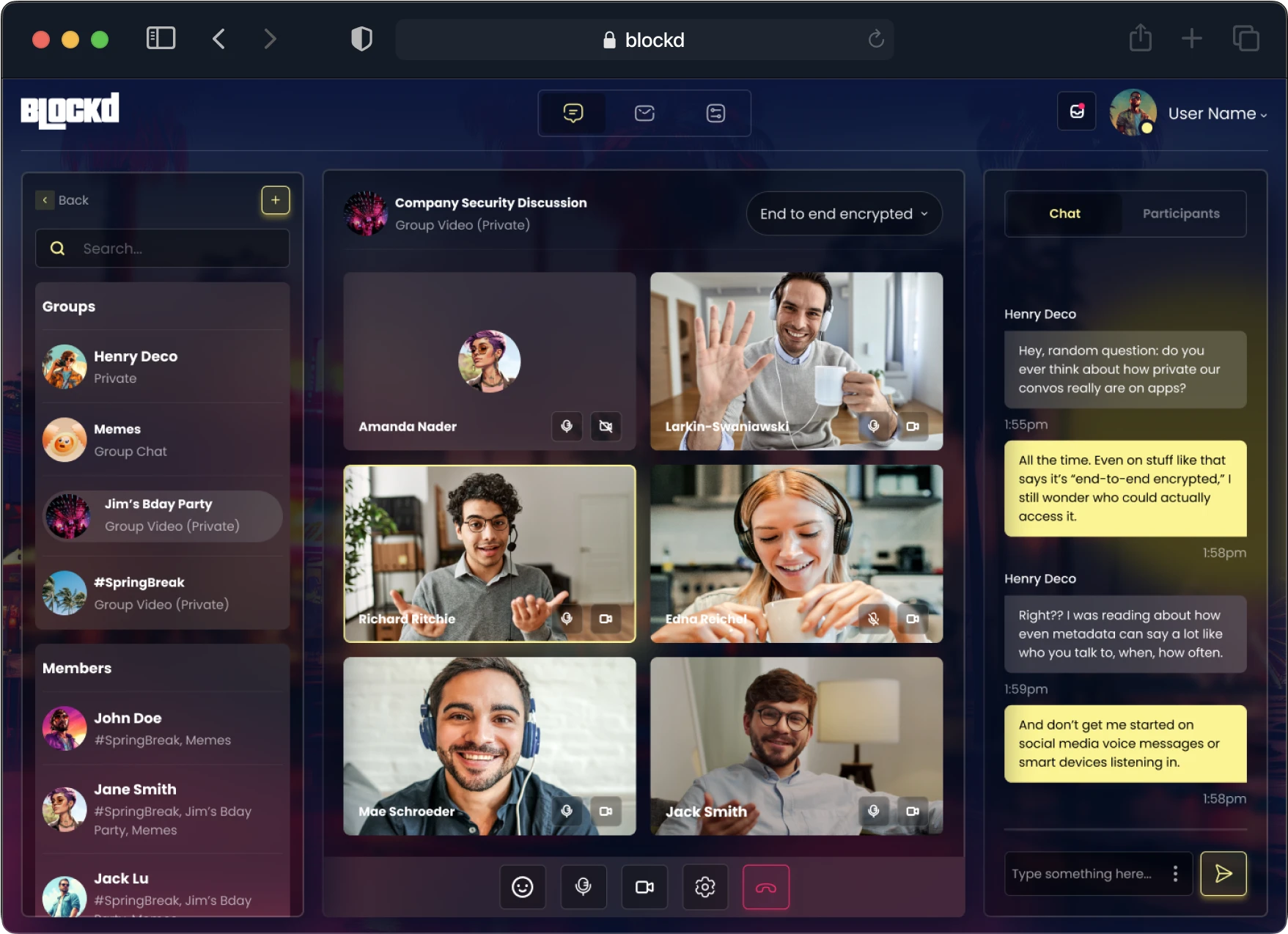
3. Decentralized Relays: No Single Point Of Surveillance Or Failure
Centralized messaging is easy to use, and just as easy to surveil. DarkMesh takes the opposite route, distributing message relays across a global network so that no single server has a complete picture of who is talking to whom.
Each relay only sees encrypted fragments and local routing decisions, which makes large-scale correlation or censorship significantly harder.
Why Decentralization Matters For Untraceable Messaging
When all your conversations pass through a few corporate data centers, governments and attackers know where to aim their subpoenas and exploits. With DarkMesh, there is no central hub that maps the entire network.
Decentralized infrastructure also supports resilience. If one region or provider is pressured or compromised, the network can route around it instead of failing wholesale.
- Global relay distribution prevents jurisdictional chokepoints.
- Encrypted routing metadata hides who is sending and who is receiving at each hop.
- Censorship resistance because blocking would require tracking and filtering across many independent relays.
Decentralization Paired With User Control
DarkMesh does not just hide the network from adversaries. It also gives you options. You can choose how your messages are stored, and which network paths they take, balancing speed, anonymity, and your personal threat model.
This level of configurability is what moves Blockd beyond one-size-fits-all privacy, and into user-controlled communication infrastructure.

Discover how DarkMesh Protocol enhances privacy with untraceable messaging. This infographic highlights the top five benefits.
4. Tor-Inspired Onion Routing, Without The Guesswork
Onion routing is a proven way to obscure who is talking to whom, and about 2.5 million people already rely on the Tor network daily. DarkMesh embraces that maturity instead of reinventing a weaker, proprietary clone.
We leverage the actual Tor network as an option, meaning you can route messages through a system that has been battle tested for years, not an experimental side project.
How Onion Routing Protects Your Metadata
Every DarkMesh Tor-style circuit wraps your traffic in multiple layers of encryption, each peeled off by a different relay. No single relay ever sees the whole picture, only where to send the packet next.
This protects the two most sensitive metadata points in any conversation: your IP address and your recipient’s IP address.
- Multi-hop routing makes it extremely costly to correlate sender and recipient.
- Randomized paths break repeatable patterns that could identify you over time.
- Protocol-level obfuscation prevents simple DPI-based blocking of DarkMesh traffic.
Speed, Latency, And Realistic Expectations
Multi-hop routing has costs. Research shows that multi-hop paths can add 100 to 500 milliseconds per hop, and typical speeds may drop to 10 to 50 Mbps, depending on the network.
Our job with DarkMesh is to give you clear choices, so you can decide when you need maximum anonymity and when a lighter route is acceptable.
Did You Know?
Surveys indicate 40–60% of US privacy-tool users report speed reductions of 20–50% when using multi-hop routing, and about 25% abandon such tools due to latency.
With DarkMesh, we acknowledge these tradeoffs and give you the steering wheel instead of locking you into one rigid configuration.
5. Metadata Defense: Because Content Encryption Is Not Enough
End-to-end encryption is now table stakes, but it does not stop apps from logging who you contact, when, where from, and how often. That data alone can map your relationships, habits, and movements with frightening accuracy.
DarkMesh treats metadata as toxic waste. Our job is not just to encrypt it, but to minimize, fragment, and obfuscate it until it is practically useless to an adversary.
How DarkMesh Cuts Your Metadata Trail
We do not tie your account to phone numbers or emails, so your legal identity is never the starting point. From there, DarkMesh obscures IPs, randomizes routing, and strips out nonessential headers that usually feed analytics and surveillance systems.
We also design the protocol so that time, size, and frequency patterns are harder to correlate, which is where many “anonymous” tools quietly leak.
- No central contact graphs built from your address book or phone number contacts.
- No cloud backups that silently re-expose your messages to Big Tech storage systems.
- No advertising trackers or analytics code that profiles your behavior in the background.
Anonymity As A Prerequisite For Privacy
In a world where 95% of desktop sites and 94% of mobile sites contain at least one tracker, you cannot rely on content encryption alone. You need to be anonymous enough that the trackers cannot reliably say “this is you” in the first place.
That is why we see anonymity not as an optional advanced feature, but as the necessary baseline for real privacy.
6. Anonymous Accounts: No Phone Numbers, No KYC, No Backdoor Identifier
Most “private” messengers compromise anonymity at the first step, by forcing you to link a phone number or email, then keeping that mapping indefinitely. DarkMesh does not have that anchor, because Blockd accounts do not require KYC-style identifiers at all.
We believe that in the current environment, anonymity is not extreme, it is necessary if you want genuine privacy.
Why We Refuse To Tie You To A Phone Or Email
Phone numbers are government and telecom controlled. They are easy to hijack, subpoena, or quietly monitor. Email is not much better, since it often sits on centralized servers that cooperate with data sharing requests.
By avoiding both, DarkMesh operates in a world of pseudonymous keys and seed phrases, not in a world of SIM cards and corporate inboxes.
- No SIM, no surveillance trail connecting your account to your real-world subscriber record.
- No recovery by SMS or email, so these channels cannot be used as attack vectors.
- Seed phrase recovery so you can regain access without exposing your identity.
Countering The “Nothing To Hide” Fallacy
We reject the idea that only criminals care about anonymity. With 53.3 billion identity records recaptured in a single year, ordinary users have more than enough reason to avoid being permanently tagged and profiled.
DarkMesh gives you a way to speak freely without handing over the keys to your offline life.
7. Configurable Storage: From On-Device Only To User-Owned Cloud
Untraceable messaging is not just about how packets move. It is also about where messages rest, and who controls that storage. DarkMesh works hand in hand with Blockd’s flexible storage options to keep you in charge.
You can decide whether messages live only on your device, for a short time on our infrastructure, or in the future, on user-owned blockchain storage like ICP.
Storage Options That Match Your Risk Model
Different conversations have different lifespans. A high-risk discussion might need true ephemerality, while a business workflow might require longer retention under your control.
We let you choose between:
- On-device only storage for maximum control and minimal external footprint.
- Temporary or ephemeral storage where messages auto-expire after defined windows.
- Blockd cloud for convenience, still covered by our privacy-by-design principles.
- Future ICP blockchain option where storage is user-owned and cryptographically governed.
Secure Re-Encryption For Closed Conversations
We also treat your conversation lifecycle seriously. When you close a thread, DarkMesh helps ensure that old messages are re-encrypted appropriately, limiting their exposure on disk and in memory.
This makes casual device access, or forensic scraping of old threads, far less useful as an attack path.
Did You Know?
Over 80% of people worry about how their personal data is used online, yet most still rely on apps that copy their entire chat history into cloud backups.
DarkMesh combined with our storage model is designed to ensure that, if something does not need to exist, it does not.
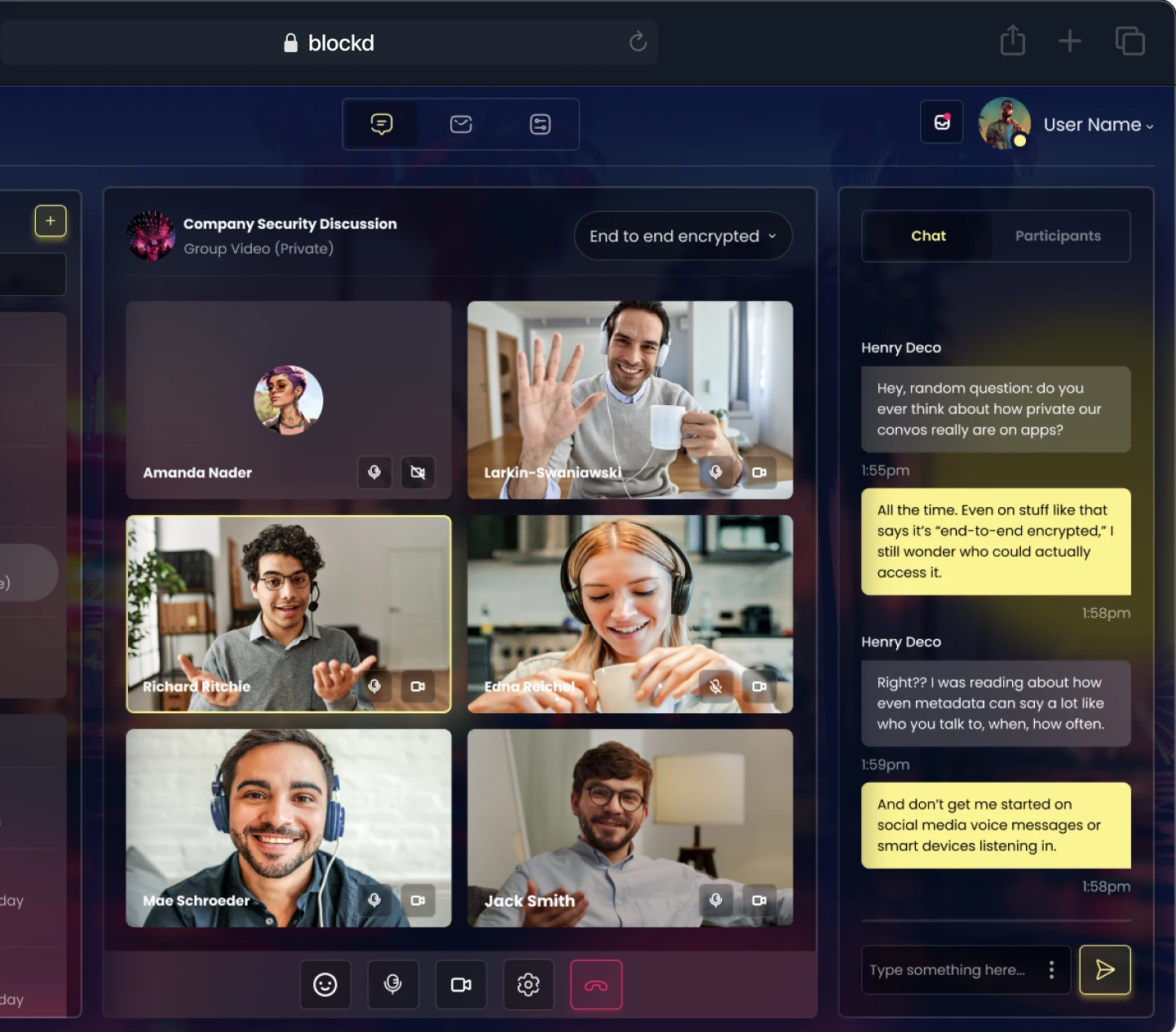
8. Network Flexibility: Route Through Blockd Or Tor As Needed
Different contexts require different routing choices. Sometimes you want the lowest latency, other times you want the strongest anonymity you can get, regardless of speed.
DarkMesh is unique in giving you the ability to send messages either through Blockd’s distributed servers or the Tor network itself. No other mainstream messaging app has achieved this dual-path design.
Choosing Your Path Without Losing Security
Whether you tunnel through our infrastructure or Tor, DarkMesh maintains end-to-end encryption and the same key handling principles. The difference is in the path, not in the cryptography.
On less sensitive traffic, Blockd routing can provide a smoother experience. For high-risk communication, Tor routing adds additional layers of anonymity on top of what DarkMesh already provides.
RouteTypical BenefitTradeoffBlockd serversBetter speed and responsivenessSlightly less anonymity than Tor, still highly privateTor networkMaximum anonymity and routing obfuscationMore latency, dependent on global Tor conditions
Realistic Privacy For Real People
Academic models often assume perfect users who are willing to sacrifice everything for privacy. Real users are not like that, and they should not need to be.
DarkMesh’s routing flexibility is designed to keep high privacy within reach for everyday use, rather than pushing it into niche, unusable extremes.
9. Pragmatic Security: Private Without Pretending To Be Perfect
We are clear about one thing: DarkMesh is built to resist strong adversaries, but no system is magically invincible. What matters is how many realistic attack paths it closes and how transparent we are about tradeoffs.
That is why Blockd is not currently open source. At this stage, exposing early code would hand attackers a blueprint before the protocol has matured, which would undermine the very users we aim to protect.
Why We May Open Source Later, But Not Yet
Open source has clear benefits, but only when a system is stable enough that public scrutiny helps more than it harms. In early phases, many projects expose half-baked code, and attackers exploit those gaps long before defenders can react.
We are not willing to use our users as test subjects in that way. Open sourcing may be considered in the future, but it is not on the short-term roadmap.
- Focus on hardening DarkMesh against practical, real-world attacks first.
- Iterate responsibly before inviting large-scale adversarial review.
- Align disclosure with maturity, not with marketing timelines.
Security Culture Built Around User Empowerment
Our background is not Silicon Valley hype. We come from cannabis regulation, decentralization, and cryptography, where real-world consequences of surveillance are obvious.
That perspective shapes how we design DarkMesh, our tolerance for risk, and our refusal to compromise on fundamentals like anonymity and data minimization.
10. A Future-Proof Foundation For Free Speech And Resistance
DarkMesh is not a toy protocol. It is designed as a long-term foundation for people who need private, untraceable communication to do their work, live their lives, or organize without fear.
From activists and journalists to regulated industries and ordinary citizens, the threat landscape is only getting more aggressive, not less.
Protecting Free Speech At The Protocol Level
When governments push for backdoors or silent access arrangements, they usually rely on centralized architectures and identity-bound accounts. DarkMesh undermines those assumptions by removing the leverage points they expect.
There are no master keys, no central logs, and no KYC account registry for them to quietly compromise.
- Resistant to mass surveillance because aggregation points and identifiers are missing by design.
- Resistant to censorship because routing is distributed and hard to block without collateral damage.
- Supportive of dissent, journalism, and sensitive communication that cannot survive traceable infrastructure.
Building For The Next Decade, Not Just The Next Release
Quantum-resistant encryption, seed-based recovery, and user-owned storage options are not trendy add-ons. They are our way of making sure DarkMesh stays relevant as cryptography, regulation, and network threats evolve.
We are not here to chase app store charts. We are here to give you a communication layer that respects your rights and does not crumble under pressure.
Conclusion
Untraceable messaging is no longer a theoretical problem—it is a daily necessity in a world saturated with trackers, datacenters, and identity brokers. DarkMesh is our answer: a protocol designed to keep you invisible, anonymous, and in control, from routing to storage to account creation.
If you want to live beyond the data shadow, the path forward is clear: stop handing over your metadata and identity to apps that treat privacy as a toggle, and move your communication onto infrastructure where privacy is the foundation. That is what DarkMesh is built to provide inside Blockd, for anyone who refuses to be tracked, profiled, or silenced.
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)






_thumb.png)