Metadata Privacy Encryption Beyond Message Content: Why Anonymity Is Now Non-Negotiable
WhatsApp alone processes more than 100 billion messages per day, and every one of those messages generates a metadata trail that can be profiled, correlated, and weaponized, even when the content is encrypted. In a world where your communication patterns say more about you than your words, protecting message text is not enough—which is why we built Blockd to treat metadata privacy and anonymity as the core problem, not an afterthought.
.png)
Metadata Privacy Encryption Beyond Message Content: Why Anonymity Is Now Non-Negotiable
WhatsApp alone processes more than 100 billion messages per day, and every one of those messages generates a metadata trail that can be profiled, correlated, and weaponized, even when the content is encrypted. In a world where your communication patterns say more about you than your words, protecting message text is not enough—which is why we built Blockd to treat metadata privacy and anonymity as the core problem, not an afterthought.
Key Takeaways
QuestionAnswer1. What is metadata in messaging apps and why does it matter?Metadata is the who, when, where, and how of your conversations. It exposes social graphs and behavioral patterns, which is why we focus on it in our deep dive on metadata tracking.2. Is end-to-end encryption enough to stay private?No. End-to-end encryption protects content but not metadata. True privacy needs encryption plus anonymity, as we explain in our comparison of encryption vs anonymity.3. How does Blockd handle metadata differently from legacy apps?We minimize what exists, decentralize what must exist, and encrypt the rest, which we break down in our architecture overview.4. Why is anonymity necessary for metadata privacy?If your identity is tied to a phone number or email, your metadata trail can be linked back to you. We explain why anonymity is required for true invisibility in our anonymity guide.5. What role does decentralized routing play in metadata protection?Decentralized, Tor-style routing breaks the link between sender and receiver, as we describe in our DarkMesh architecture article.6. Are “zero-data” claims enough to guarantee privacy?Zero-data without strong anonymity still leaks metadata patterns. We unpack this tradeoff in our review of zero-data protocols.7. Where can I explore more on metadata-focused privacy?Our full blog at Blockd Signals covers metadata privacy, DarkMesh, and anonymity-first design in detail.
Why Metadata Privacy Matters More Than Encrypted Content
Most modern messengers advertise end-to-end encryption, yet 11 of 21 widely used secure messaging apps still leak metadata in push notifications, and several even leak message content at that layer. This gap exists because the industry has treated content encryption as the finish line, while quietly ignoring the far richer data trail around every message.
Metadata is not a side channel—it is the main signal used to reconstruct who you are, who you talk to, when, how often, and from where. When you add identity-bound onboarding like phone numbers, email, or KYC, the metadata trail stops being abstract and becomes a concrete map back to a real person.
What “Metadata Privacy Encryption” Really Means
When we talk about metadata privacy encryption beyond message content, we mean encrypting, obscuring, and minimizing all the layers around the message body itself. This includes routing information, device identifiers, contact graphs, timestamps, and storage locations.
At Blockd, our approach is simple and uncompromising: encrypt what we must keep, avoid collecting what we do not need, and separate any necessary technical metadata from human identity entirely.
Blockd’s Mission: Privacy First, Identity Optional
We built Blockd around a principle that should be obvious but is still rare: privacy cannot depend on users handing us their identity. No phone numbers, no emails, no KYC, no hidden identity linkage behind the scenes.
You decide what exists, and for how long. If a piece of metadata is not required for delivering a message, we design the protocol so that it never exists in the first place.
Metadata Explained: The Invisible Trail That Outs You
Metadata is everything around your message that is not the message body itself. It includes sender and receiver identifiers, IP addresses, timestamps, group membership, device fingerprints, and how often you open the app.
Individually, these fields may seem harmless. Combined and analyzed at scale, they form a behavioral fingerprint that is often more identifying than any single data point, which is why profiling companies and state-level actors invest heavily in metadata analysis.
How Legacy Messaging Apps Leak Metadata
Even popular encrypted messengers often leak metadata through push notifications, contact discovery, logging, and centralized analytics. If your account is tied to a phone number, that trail is immediately linked to a real-world identity that is easy to subpoena, breach, or cross reference with other datasets.
Cloud backups and cross-device sync make the problem worse because they freeze your communication history into permanent, centralized records. Deleting the app does not delete the metadata trail that has already been harvested.
Why Anonymity Is Now a Requirement, Not a Preference
In a world where metadata is the dominant surveillance channel, being anonymous is not a luxury for activists or journalists. It is a baseline requirement for anyone who does not want their personal life, relationships, or habits profiled and traded.
Our stance is straightforward: as long as your messaging identity is keyed to your phone number, email, or KYC record, true metadata privacy is impossible. The only honest answer is to remove that linkage entirely.
End-to-End Encryption vs True Anonymity: Why You Need Both
End-to-end encryption ensures that only the sender and receiver can read the content of a message. It does not, by itself, hide that a message was sent, who sent it, who received it, when, or through which servers it passed.
True anonymity targets those surrounding signals. It breaks the direct link between identity and communication behavior, so even if someone inspects the network or servers, they cannot reliably map flows back to specific people.
Where Encryption-Only Approaches Fall Short
An encrypted messaging app that requires a phone number already starts from a compromised baseline. Even if the provider cannot read your messages, they can often map account identifiers to real-world identities and share that information under pressure.
Metadata-based correlation can reliably reveal your social graph and interaction patterns without ever decrypting a single payload. If your goal is to stay invisible, that is not acceptable.
How Blockd Combines Encryption and Anonymity
We use strong, modern cryptography, including a quantum resistant NaCl based algorithm, to protect content and metadata fields that must exist temporarily for delivery. Keys are stored client side, never held centrally in a way that could be mass harvested.
At the same time, we eliminate identity linkage by design. No phone number. No email. No KYC. Your presence in the network is defined by cryptographic keys and seed phrases, not by personal identifiers that can be tied back to you.
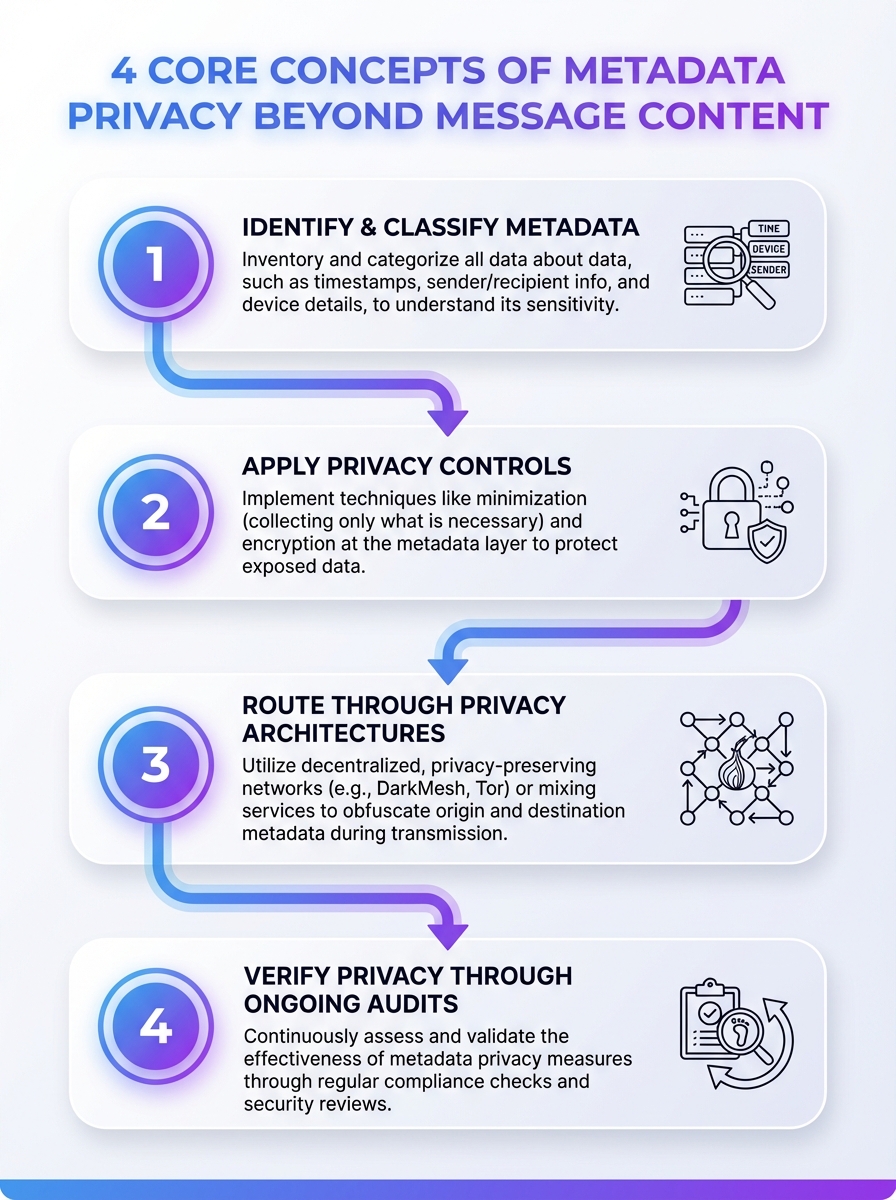
This infographic breaks down four core concepts of protecting metadata privacy beyond the message content. Learn how encryption and privacy-by-design approaches safeguard metadata usage.
Inside DarkMesh: Metadata Privacy Built Into the Network Layer
DarkMesh is the hidden architecture that sits under Blockd. It is how we route messages, distribute relays, and structure encryption layers so that your communications are untraceable, your identity is invisible, and your metadata is hardened against correlation.
Instead of relying on a single central server that sees everything, DarkMesh uses a decentralized, peer assisted network of relays that never have a full picture of who is talking to whom.
Zero-Knowledge Design: We Know Nothing, So Nothing Can Be Taken
DarkMesh follows zero knowledge principles. Every message, identity, and metadata layer is encrypted, hashed, and salted in a way that prevents us from reconstructing meaningful user profiles, even with full access to our own infrastructure.
We architect the system so that there is no door to unlock. No retained keys, no identity logs, no central contact lists, and no dependency on third party notification services that leak metadata.
Onion-Style Routing Over Tor: Separating Sender and Receiver
DarkMesh leverages the actual Tor network, not a weaker in house imitation, to route traffic through multiple anonymous relays. Each hop peels away a layer of encryption, but no single node ever learns both the origin and final destination.
This onion style routing severs the straightforward mapping of IP to account. Even a powerful adversary that can watch parts of the network will struggle to correlate flows and reconstruct your social graph.
Did You Know?
Under typical data retention regimes, metadata-based correlation can reliably link caller and callee flows, revealing edges in users’ social graphs without decrypting payloads.
Centralized vs Decentralized Privacy Infrastructures
Centralized privacy tools still ask you to trust a single provider with your biggest risk: the ability to see or reconstruct your communication graph. Even when they promise not to log, the architecture itself creates a tempting single point of failure.
Decentralized messaging infrastructures flip this model. They distribute trust and capability across multiple nodes, so no single operator, breach, or subpoena can expose a complete picture of your activity.
Why Centralization Quietly Destroys Metadata Privacy
Centralized systems naturally accumulate logs, analytics, and technical telemetry. Over time, those artifacts become an unintentional metadata archive, even for companies that never planned to surveil their users.
When you combine that with real-world identity onboarding, you end up with a communication history that is easy to request, breach, or correlate with other datasets, long after you thought you had deleted it.
How Blockd Uses Decentralization to Sever Trails
We design DarkMesh as a decentralized, relay based network, and we give users control over how their traffic is routed. You can send messages through Blockd relays, over Tor, or a combination, depending on your threat model and performance needs.
Because we do not centralize identity or store clear text data on our servers, external pressure hits architectural limits. There is simply less to take, less to correlate, and less to leak.
Zero-Data vs Zero-Privacy: The Limits of “We Store Nothing”
Zero-data messaging protocols promise not to retain user data, logs, or content beyond what is required for live delivery. That is a good start, but it is not a complete answer to metadata privacy.
If a protocol still relies on identity based registration, static network identifiers, or centralized routing, then even a zero-data provider can leak behavioral metadata to observers who sit outside the system.
Layered Messaging: Stacking Defenses Against Metadata Correlation
We view metadata privacy as a layered problem that needs layered defenses. Content encryption, routing obfuscation, decentralized relays, and identity free onboarding all work together to minimize what can be correlated.
It is not enough to say “we do not log.” We ask a harder question: if an adversary observed your traffic over time, could they still infer who you are or who you are talking to, even without our help.
Blockd’s Practical Zero-Data Approach
Our goal is simple: if someone breaches our infrastructure, they should find encrypted blobs and no meaningful personal data. That is why user keys live on device, messages can be stored locally or ephemerally, and we avoid building central archives.
We also support secure re encryption of messages at rest, so that even on your own device, messages are locked until you reopen a conversation. This restricts the blast radius of device compromise and physical access.
Configurable Storage: On-Device, Ephemeral, Cloud, or User-Owned
Metadata privacy is not just about how messages move. It is also about where they live, who controls that storage, and how long records persist. Giving users no choice here is a design failure.
We treat storage location and retention as user controlled levers. You choose if your data lives only on your device, temporarily on our infrastructure, or in user-owned environments.
Your Storage Options in Blockd
- On-device only: Messages never leave your device except in encrypted transit and are not persisted on our infrastructure.
- Temporary or ephemeral: Messages exist on relays only as long as needed for delivery, then expire automatically.
- Blockd cloud: For users who want portability, we offer encrypted cloud storage where we cannot read your content.
- Future ICP blockchain: We are exploring user-owned storage on decentralized compute platforms, so your data lives under your keys, not our accounts.
This configurability means you decide how much of a footprint you want. High risk users can bias toward ephemeral, device only patterns, while others can trade controlled persistence for convenience without giving up control.
Re-encrypting Conversations at Rest
To further narrow metadata exposure on your own device, Blockd can re encrypt conversations when you close them. Messages stay locked behind your passkey and are decrypted only on demand.
Combined with passkeys stored on device and seed phrase based account recovery, this gives you strong local security without handing us recovery secrets or persistent identity anchors.
Did You Know?
189 participants completed a vignette-based survey on user perceptions of untraceability in messaging platforms, highlighting how differently people think about metadata privacy beyond message content.
No Phone Numbers, No KYC: Why Anonymous Onboarding Matters
Almost every mainstream messenger uses your phone number or email as the root of your identity. It is convenient, but it is also a direct, permanent bridge between your private communication and your public, regulated identity.
If you care about metadata privacy, that tradeoff is unacceptable. Convenience should not mean your social graph is one subpoena, breach, or cross reference away from full exposure.
How Identity Linkage Amplifies Metadata Risk
Once your account is linked to a phone number, everything else becomes trivial. Data brokers, advertisers, and investigative bodies already use phone based datasets as cross referencing keys across apps and services.
That means your supposedly protected messaging metadata can be combined with location data, purchase histories, and social media activity to build a precise profile you never consented to.
Blockd’s Anonymous-by-Default Account Model
We do not require phone numbers, emails, or any form of KYC to use Blockd. Your account is defined by cryptographic material that you generate and control locally, plus a seed phrase that lets you recover it if needed.
Passkeys stay on your device. Account recovery does not go through us. Because we never hold personally identifiable information, there is nothing for us to leak, sell, or hand over that links your communications to a real world identity.
Routing Over Tor vs Proprietary “Anonymity Layers”
Some platforms advertise proprietary anonymity layers without the maturity, peer review, or ecosystem support that battle tested networks like Tor provide. When your safety depends on anonymity, experimental routing is not enough.
We chose to integrate with the actual Tor network because it has been hardened over decades, analyzed rigorously, and deployed at global scale. It is not perfect, but it is real infrastructure, not marketing.
Why Tor Matters for Metadata Privacy
Tor separates your IP address from the services you talk to by routing traffic through multiple volunteer operated relays. No single relay sees both your origin and your destination, which drastically raises the cost of correlation.
For metadata privacy, this matters more than yet another crypto primitive. It changes the network level visibility adversaries have into who you are talking to and from where.
Giving Users Choice: Blockd Relays or Tor
We do not assume every user has the same threat model. Some will prioritize maximum anonymity and choose Tor routing for all traffic. Others will prefer a mix of Blockd relays and Tor, balancing latency with invisibility.
What we refuse to do is lock you into a single path that quietly optimizes our costs while increasing your risk. Configurability is not a bonus feature. It is how we respect different privacy needs in the real world.
How Blockd Protects You From Everyone, Including Us
We design Blockd so that trusting us is optional. Our architecture, policies, and product decisions aim to minimize the damage we could do, even if we wanted to, and to limit what any attacker or regulator could extract.
That is what privacy by design actually means: building systems where intentions matter less because capabilities are constrained up front.
Our Zero-Trust Principles in Practice
- No PII collection: No phone numbers, emails, or KYC in the core product.
- Client-side keys: Encryption keys are generated and stored locally, not centralized.
- No unencrypted user data at rest on our servers: Breaches yield encrypted blobs, not chat logs.
- Minimal retention: Metadata is not archived long term unless strictly needed, and you control storage preferences.
We are also intentionally not open source at this early stage, to avoid exposing immature code to exploitation before the architecture has been fully hardened. Open sourcing may be considered later, but we will not pretend that code transparency alone guarantees safety.
Legal Pressure and “Back Door” Mandates
Because we decentralize identity and keep no central archives of who talks to whom, most conventional backdoor requirements lose their practical impact. There is no giant user directory to hand over, and no clear text logs to mine.
We cannot promise that the legal landscape will never change, but we can design our system so that your safety does not depend entirely on our legal resistance. If your data never sits on a corporate disk in readable form, it cannot be used against you later.
Conclusion
Metadata privacy encryption beyond message content is not a slogan for us. It is the recognition that in modern surveillance ecosystems, who you are, who you know, and how you behave can be reconstructed without ever reading your words.
Our answer is to combine strong cryptography, real anonymity, decentralized routing over Tor, configurable storage, and anonymous onboarding into one coherent system that keeps you invisible by default.
Speak freely. Stay private. Let your metadata trail go dark.
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)






_thumb.png)